Table of Contents
- The Password Problem: Why We Need Better Solutions
- Understanding Biometric Authentication Types
- The Security Advantage: More Than Convenience
- Designing Biometric Authentication: UX Best Practices
- Implementation Considerations for Designers
- Measuring Success: Biometric Authentication Metrics
- The Future of Biometric Authentication
- Conclusion: Balancing Security and Simplicity

Biometric authentication in apps uses your fingerprint or face to verify your identity instead of a password. It is best added after a user's first login, should always be optional, and must include a password or PIN as a fallback. The biometric data never leaves the user's device the app only receives a pass or fail signal from the operating system.
If you design mobile apps, you’ve already worked with biometric login. Fingerprint and face authentication are everywhere now, and users expect them to just work.
The problem is, biometric authentication is easy to add and easy to mess up. It lives right at the start of the experience, where users decide whether an app feels fast, safe, or broken. Small UX decisions here make a big difference.
This guide is about designing biometric authentication in apps the right way. We’ll cover how it works at a high level and how to design login flows .
Why Do Apps Use Biometric Authentication?

Biometric authentication is a way to confirm who someone is by using their body, not their memory. This usually means a fingerprint or face scan. Instead of typing a password or PIN, the device checks these signals and decides if access should be allowed.
Passwords don’t work well in daily life. People forget them, reuse them, or choose weak ones. PINs and patterns add extra steps but don’t always make things safer. When security feels hard, people look for shortcuts.
Biometric authentication reduces this problem. It lets people unlock devices and apps quickly without needing to remember anything. This makes secure actions easier to complete, and security only works when people actually use it.
Why Do Some Users Distrust Biometric Login?
Even when biometric authentication works perfectly from a technical standpoint, some users still resist enabling it. Understanding why is essential for designing an onboarding experience that actually converts.The most common fear is data storage.
Many users believe their fingerprint or face scan is being uploaded to a company server somewhere. This is not how it works, but the misunderstanding is widespread. Your design has to address this directly, not assume users know the technical reality.A second concern is permanence. Passwords can be changed if they are compromised.
A fingerprint or face cannot. Users who understand this are often more hesitant than those who do not think about it at all.The third concern is surveillance. Particularly for users in certain regions or demographics, providing biometric data even to an app they trust feels like a step they cannot take back.
How to design for this: The answer is not to explain the technology in detail. It is to show users they are in control. Make enabling biometrics opt-in, show a one-sentence plain-language assurance at the moment of decision, and make it just as easy to turn off as it was to turn on. Trust is built by giving control, not by providing documentation.

Why Do Some Users Distrust Biometric Login?
Even when biometric authentication works perfectly from a technical standpoint, some users still resist enabling it. Understanding why is essential for designing an onboarding experience that actually converts.The most common fear is data storage.
Many users believe their fingerprint or face scan is being uploaded to a company server somewhere. This is not how it works, but the misunderstanding is widespread. Your design has to address this directly, not assume users know the technical reality.A second concern is permanence. Passwords can be changed if they are compromised.
A fingerprint or face cannot. Users who understand this are often more hesitant than those who do not think about it at all.The third concern is surveillance. Particularly for users in certain regions or demographics, providing biometric data even to an app they trust feels like a step they cannot take back.
How to design for this: The answer is not to explain the technology in detail. It is to show users they are in control. Make enabling biometrics opt-in, show a one-sentence plain-language assurance at the moment of decision, and make it just as easy to turn off as it was to turn on. Trust is built by giving control, not by providing documentation.
Types of Biometric Authentication
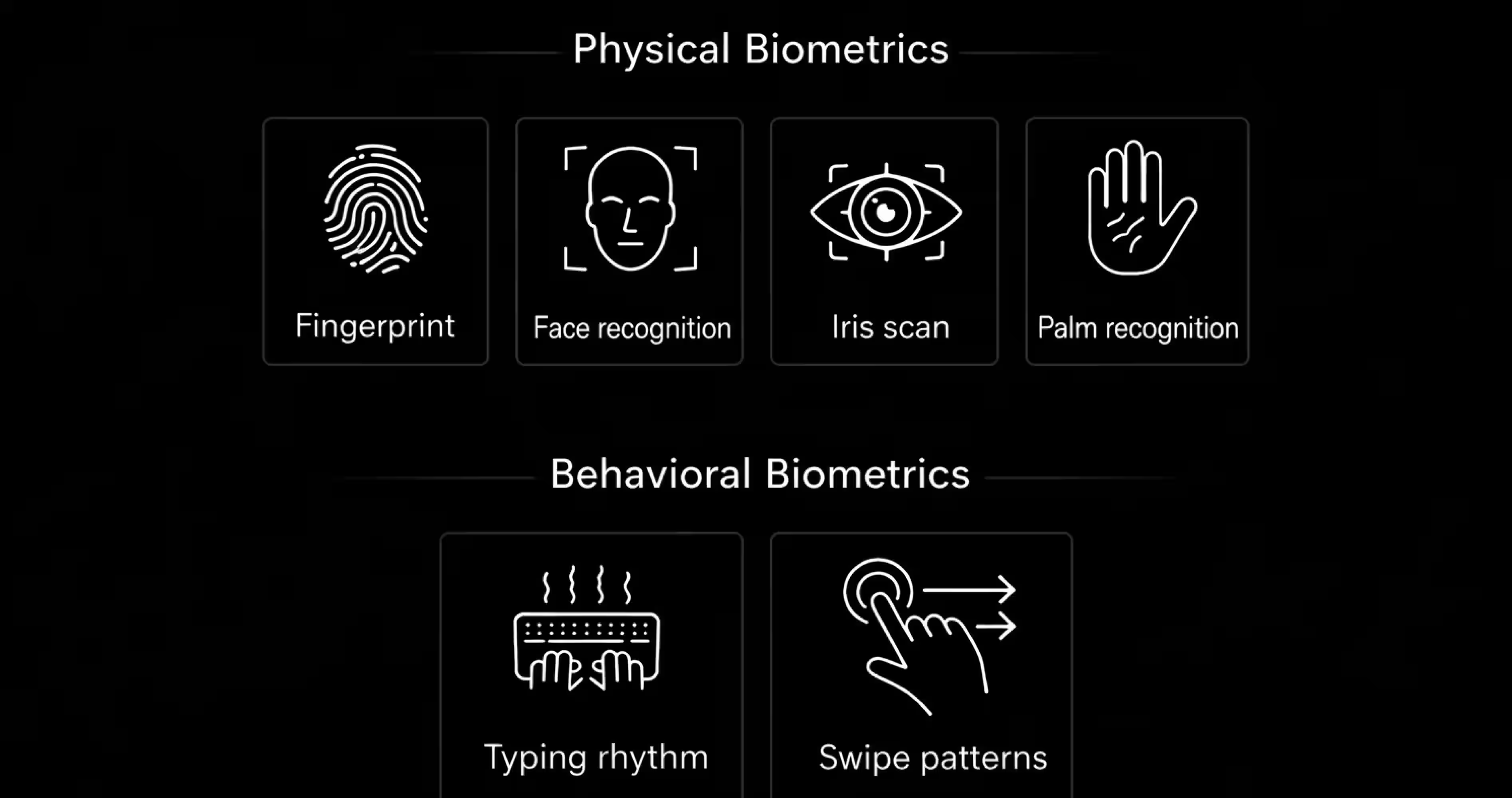
Biometric authentication is not just one method. There are different types, and each one works in its own way. Usually, biometrics fall into two main groups: physical biometrics and behavioral biometrics. Both are used to confirm who someone is, but they rely on different kinds of signals.
Here is a quick comparison of the most common biometric methods used in mobile apps today:
Physical Biometrics
Physical biometrics use physical characteristics of a person. These are traits that stay mostly the same over time and are easy for devices to capture. This is the most common type of biometric authentication used on phones and personal devices.
Fingerprint Recognition: Fingerprint authentication scans the patterns on a person’s finger and compares them to a stored reference. It’s fast, familiar, and works well for everyday use. That’s why it’s widely used for unlocking phones, apps, and payments.
Face Recognition: Face recognition uses the structure of a person’s face to confirm identity. Modern systems don’t just look at a photo, then analyze the depth, shape, and movement. This method works well when hands-free access is needed, but it depends more on lighting and camera quality.
Iris or Eye Scanning: Iris recognition uses patterns in the eye that are highly unique. It’s very accurate, but less common in consumer devices. This is because it requires specific hardware and careful positioning. You’ll usually see this in high-security environments rather than everyday apps.
Hand or Palm Recognition: Some systems use the shape of the hand or palm veins to identify users. These are reliable but less practical for mobile devices. That’s why they’re not widely used in phones.
Behavioral Biometrics
Behavioral biometrics focus on how a person behaves, rather than how they look. These signals are gathered over time instead of in a single scan.
Typing and Interaction Patterns: Some systems look at how a person types, swipes, or interacts with a device. Speed, pressure, and rhythm can form a behavioral pattern that helps detect unusual activity. This is often used quietly in the background to spot potential fraud.
Designing Biometric Authentication in Apps
Now that the basics are clear, we can focus on what actually matters: designing biometric authentication in real apps. This is where security, usability, and trust meet, and small design decisions start to have a big impact on user experience.
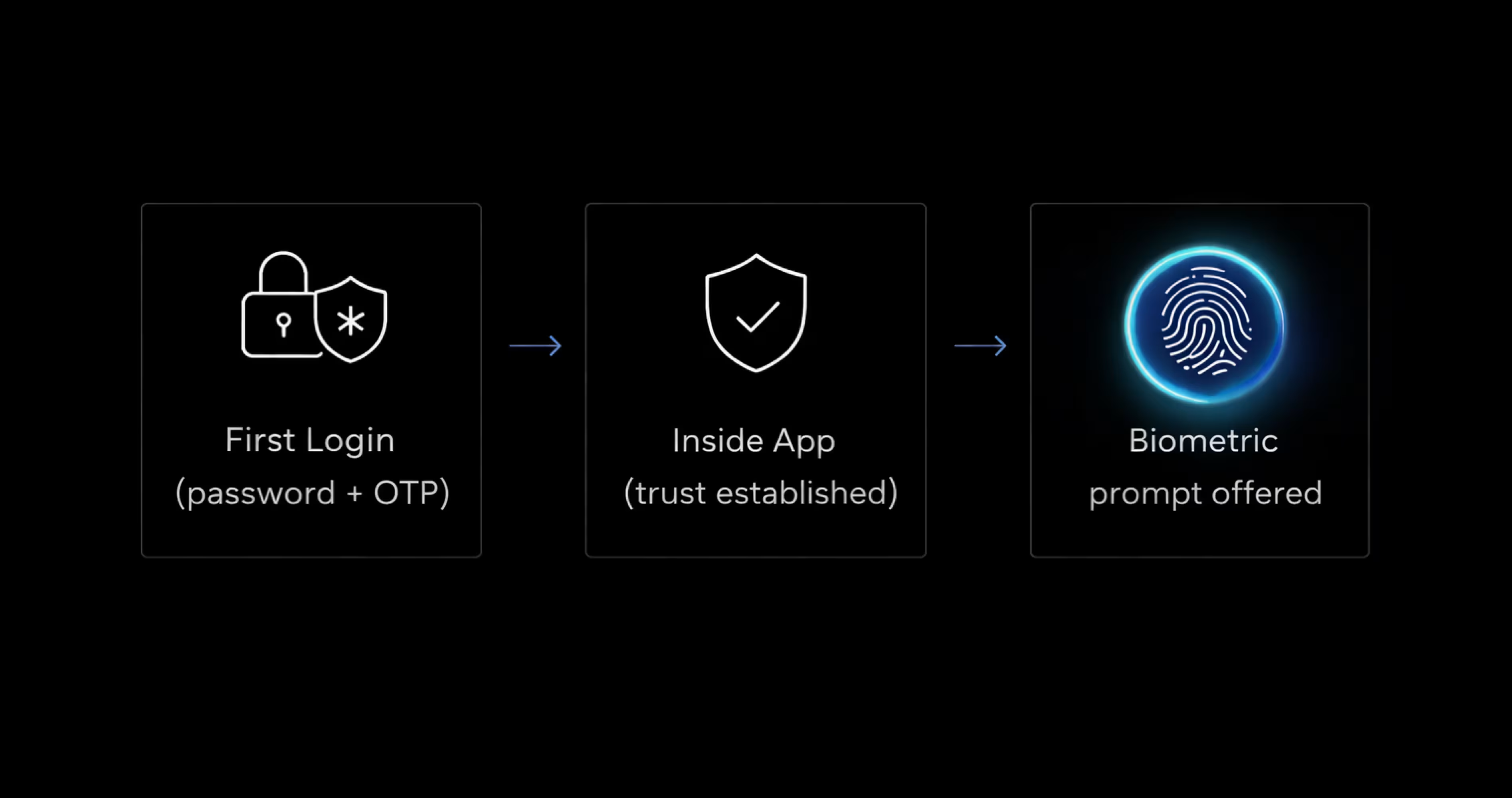
When Should an App Use Biometric Login?
If you’re planning to add biometric login to your app, it helps to understand one simple thing first: Biometric login is primarily about reducing friction. While it can give a sense of security, its main value in apps is helping users get back in quickly once trust is already established.
During the first login, users are still deciding if they trust the app. They expect clear steps like passwords, OTPs, or verification messages. At this stage, biometric login usually doesn’t help because users want to see what’s happening and feel in control.
Biometric login works best after that first login. Once users already have an account and know the app, they don’t want to repeat the same steps every time. Using a fingerprint or face scan makes getting back in faster and easier.
Security level matters here, too. For simple, everyday actions, biometric login works well. But for sensitive actions like changing account details, users often expect extra security. Using only biometrics in those cases can make people feel uncomfortable.
Always Make Biometric Login Optional
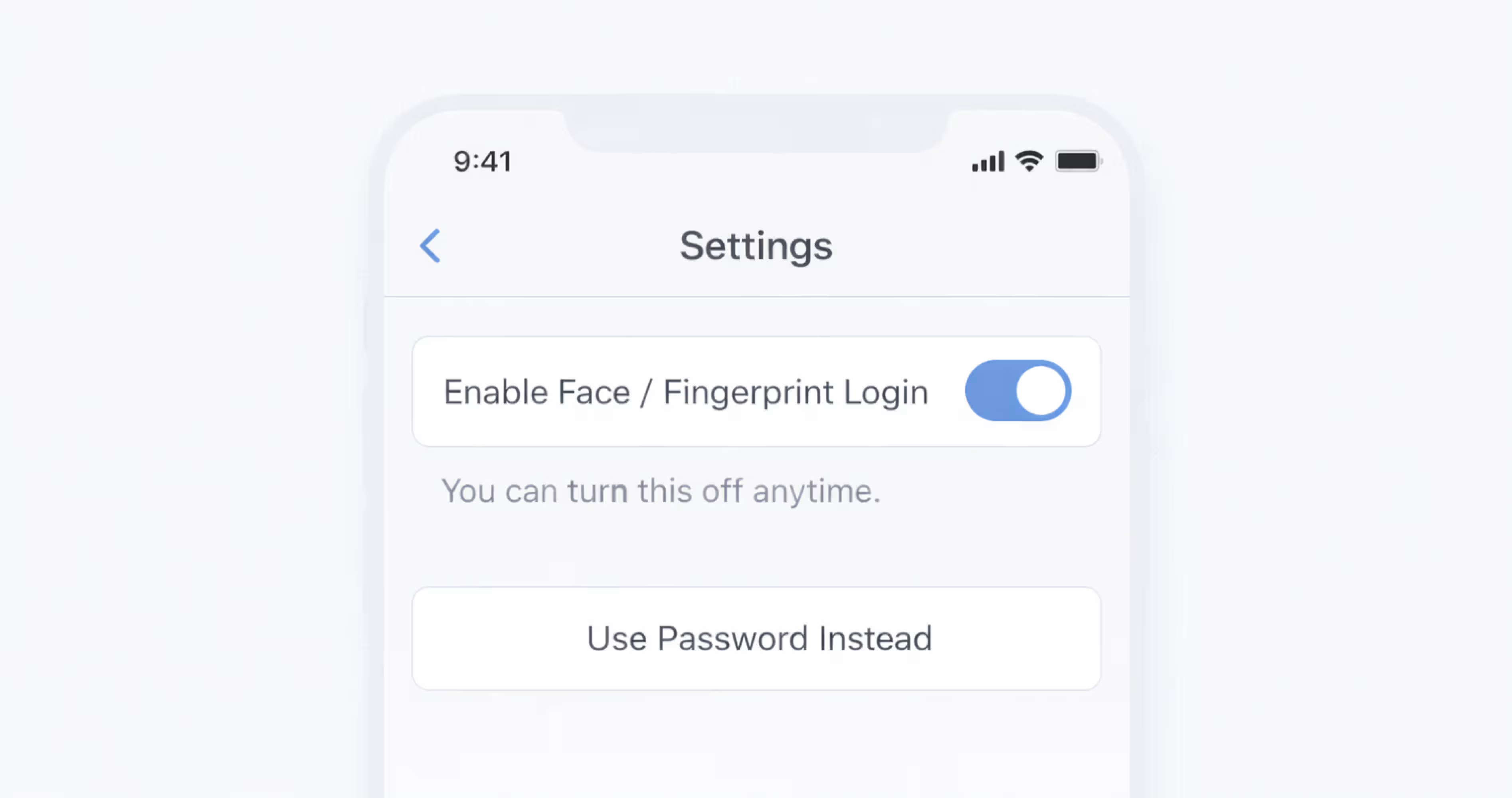
Biometric login should never be the only way to access an app. From a design perspective, forcing biometrics almost always creates more problems than it solves.
Some users don’t want to use biometrics at all. They may worry about privacy, or they may simply prefer using a password or PIN. When users feel forced to use biometrics, trust goes down instead of up.
Biometrics also don’t work for everyone. Some people can’t use fingerprints or face recognition reliably because of physical reasons. A good design makes sure these users can still log in without trouble.
Even when users want to use biometrics, devices don’t always work perfectly. Sensors fail, lighting changes, or the system doesn’t recognize the user. When that happens, users need another clear way to log in.
That’s why apps should always offer another option, like a password or PIN. This keeps users in control and makes login feel reliable instead of restrictive.
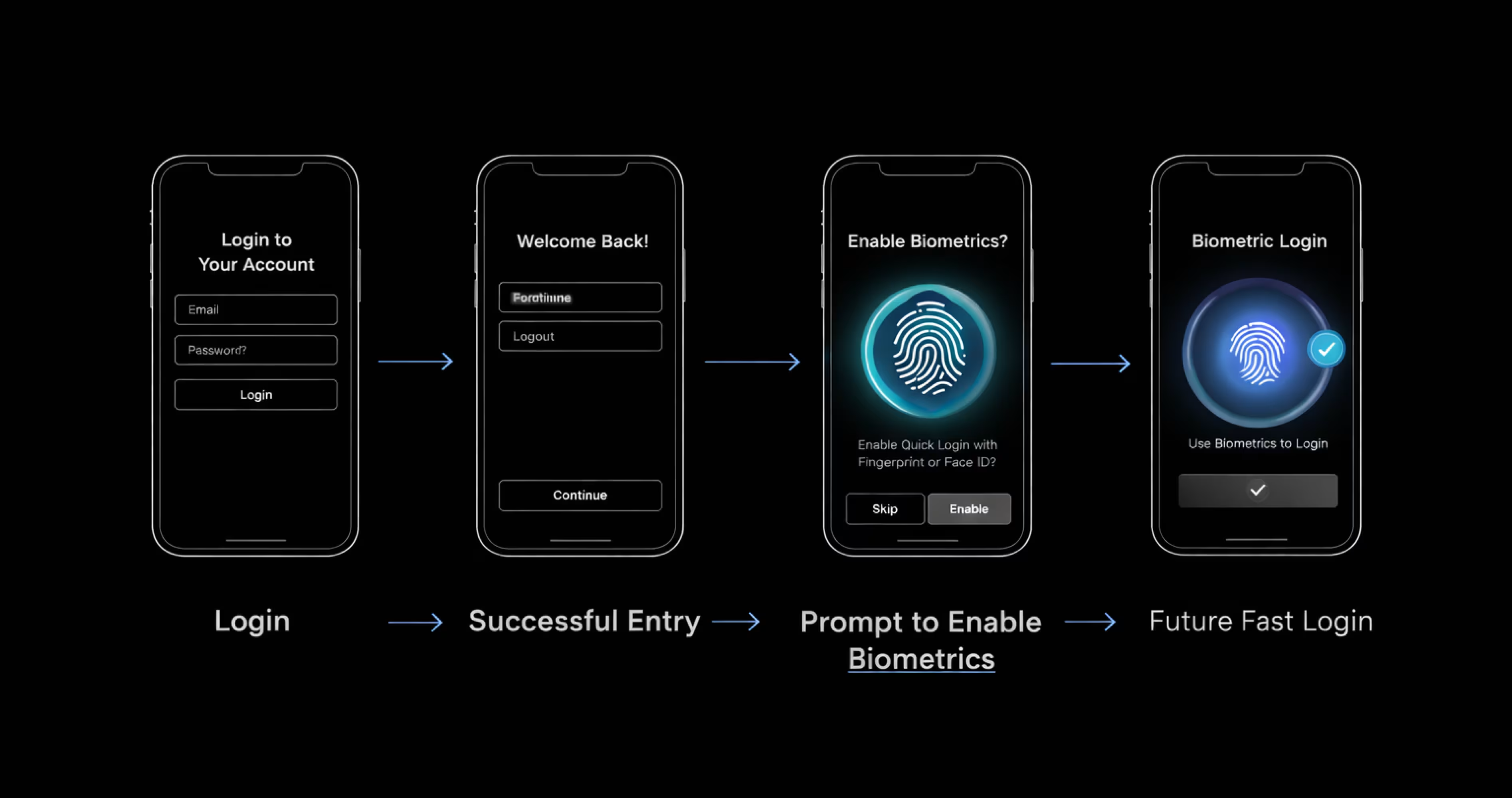
How to Ask Users to Turn On Biometric Login
The best time to ask users to turn on biometric login is after they’ve logged in successfully. At that point, they understand the app and can clearly see why faster login would be useful.
Asking too early doesn’t work well. During sign-up, before login, or right after an error, users are still figuring things out. In those moments, a biometric request can feel confusing or pushy instead of helpful.
When you ask, keep the message short and optional. Users should feel like they’re choosing this, not being forced into it. Simple wording works best, like:
- “Use fingerprint or face login to sign in faster next time?”
- “Turn on biometric login for quicker access.”
- “You can change this later.”
The main goal is to give users control. When the timing feels right and the choice is clear, users are much more likely to enable biometric login.
What to Do When Biometric Login Fails
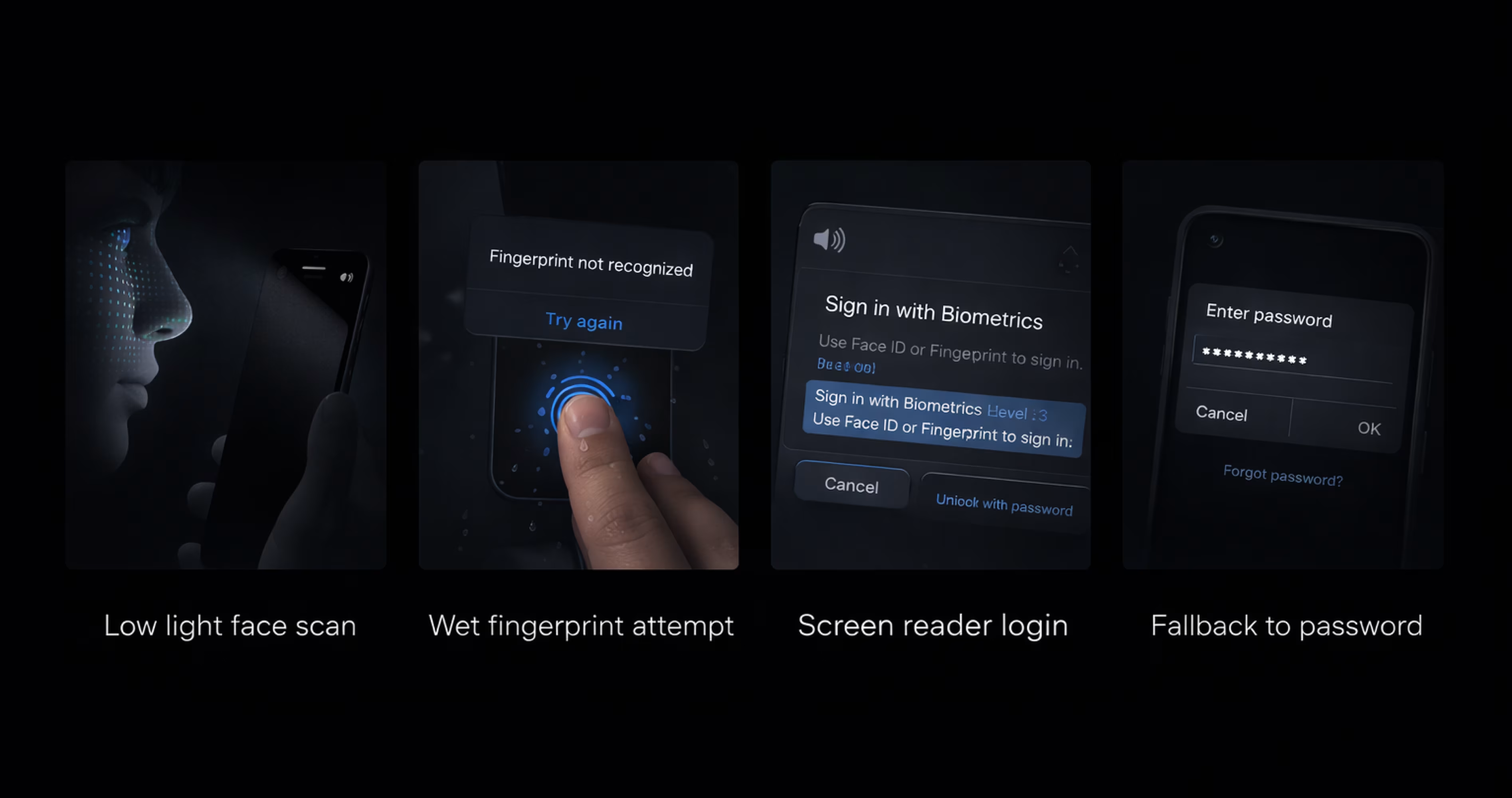
Biometric login can fail due to various reasons, such as fingers not scanning correctly, faces not being detected, or changes in lighting. None of this means that something is broken. It just means the system couldn’t be sure this time.
Because failure is expected, the design has to assume it will happen. Let users retry once or twice, but don’t trap them in a loop. Repeated retries feel frustrating fast and make the app feel unreliable.
What matters most is the fallback. When biometrics don’t work, users should immediately see another way in - a password, a PIN, or an email link. This option shouldn’t be hidden or treated like a last resort. It’s part of the normal flow.
Using Biometrics for Different Security Levels
Not everything in an app needs the same level of security. Some actions are low risk, while others need a bit more protection. Biometrics work best when they’re used only where they actually add value.
For simple things like browsing content or checking information, asking for biometrics again usually isn’t needed. Once users are inside the app, stopping them repeatedly can feel annoying.
For actions like updating profile details or changing settings, a quick fingerprint or face check can make sense. It confirms it’s really the user without slowing them down too much.
For sensitive actions like payments or changing important account details, extra confirmation is expected. In these moments, biometrics work well because users already expect an extra step for safety.
Designing Biometric Login With Privacy in Mind
When apps ask for biometric login, many users worry about one thing: what happens to their fingerprint or face data. They don’t think about how technology works. They just want to know if their data is safe.
Designers don’t need to explain technical details. What matters is explaining things in a way users can easily understand. Users want clear answers, not long explanations or legal language.
A short, direct message builds trust quickly. Something like, “Your fingerprint stays on your phone. We never see it,” is often enough to remove doubt. It tells users what they care about in plain words.
Privacy information should appear at the moment users are deciding, not hidden in settings or policies. When users understand what’s happening, they feel more comfortable turning biometric login on.
Make Biometric Login Accessible for Everyone
Biometric login is convenient, but it doesn’t work for everyone all the time. Some users can’t use fingerprint or face recognition because of physical conditions, injuries, or temporary situations.
Others may struggle because sensors fail, or the lighting is poor. A good design assumes these cases will happen.
Accessibility also means thinking about how different users move through the login flow. People using screen readers still need to understand what’s happening and how to continue. If the login flow relies too heavily on biometric interactions, it quickly becomes confusing or unusable.
This is why visible alternatives matter. Passwords, PINs, or email links should always be easy to find and easy to use. When biometric login doesn’t work, users should be able to continue without stopping to figure out what went wrong.
Common B
Most biometric UX problems don’t come from technology. They come from design decisions that ignore how people actually behave when logging in. These mistakes show up again and again, and once you see them, they’re hard to unsee.
Common mistakes designers should avoid:
- Forcing users to set up biometrics: Pushing users to enable biometrics during sign-up or blocking progress until they do usually backfires. It creates pressure instead of trust and makes users defensive.
- Hiding fallback options: Making passwords or PINs hard to find sends the wrong message. Fallbacks aren’t a failure - they’re part of a healthy login flow. If users can’t see them easily, frustration builds fast.
- Repeating failed biometric prompts: Showing the same biometric prompt over and over after failure feels broken. A couple of retries is fine. After that, users need a clear way forward.
- Locking users out too quickly: Aggressive lockouts after a few failures punish normal behavior. Biometrics fail for many harmless reasons. Lockouts should be rare, not the default response.
Platform Rules Designers Need to Know (iOS and Android)

Biometric authentication doesn’t work the same way across platforms, and designers don’t have full control over it. Most of the biometric experience is owned by the operating system, not the app. Knowing these rules helps you design flows that feel correct instead of fighting the platform.
iOS for Face ID and Touch ID
On iOS, biometric authentication is handled entirely by the system through Apple Face ID & Touch ID. The prompt, animation, and wording all come from the OS.
As a designer, you’re not expected to design the biometric screen itself. Apple wants users to see the same trusted system prompt everywhere. Custom biometric screens on iOS usually raise trust issues and can even get rejected during review.
Your role on iOS is to decide:
- When the system prompt appears
- How do you explain biometrics before asking
- What happens after success or failure
Android: Biometric Prompt
Android works in a similar way but with more device variety. Apps use the Google Android Biometric Prompt, which provides a system-level biometric dialog.
The prompt may look slightly different depending on the device, but the rules are the same. Designers shouldn’t replace it with a custom UI. Users trust the system prompt because it feels consistent across apps.
On Android, designers should focus on:
- preparing users before the prompt appears
- handling different outcomes clearly
- making fallback options easy to access
How to Test Biometric Authentication UX
Biometric login often looks fine in ideal conditions, but real users don’t live in ideal conditions. Testing is about finding the moments where things break, confuse users, or slow them down. That’s where most biometric UX problems actually come from.
Things to test before shipping:
Testing failure cases on purpose: Let biometric login fail and see what the user sees. Check whether messages make sense, retries feel reasonable, and the next option is obvious
Testing in bad lighting or noisy places: Try low light, bright light, background noise, awkward angles, or wet fingers. These situations happen all the time and often reveal problems hidden in clean test environments.
Accessibility testing: Some users can’t use fingerprint or face recognition reliably. Make sure the app still works smoothly with other login methods and doesn’t block or frustrate them.
Testing fallback flows: When biometrics don’t work, users should move to passwords, PINs, or email links without hesitation. If fallback feels hidden or slow, the experience breaks quickly.
Testing recovery after errors: Watch what users do after something goes wrong. Do they know what to try next, or do they pause and hesitate? That moment tells you a lot about your design.
Final Thoughts
Designing biometric authentication is mostly about the edge cases. We talked through when to use it, when to avoid it, how to handle failure, and how to keep users in control. Getting these right makes a big difference in how trustworthy the app feels.
The main idea is simple: biometric authentication works best when it saves time without taking control away from users. It should help users get back into the app quickly, not make them stop and think.
If you’re designing or improving a biometric login, start small. Add it after the first login, keep the wording clear, test what happens when it fails, and always include a fallback. Try it yourself in real situations and see how it feels.
Frequently Asked Questions
Is biometric authentication safe?
Yes, for everyday use, it’s considered safe. It adds a layer of protection and makes access harder for someone else, especially compared to weak or reused passwords.
Does an app store my fingerprint or face?
No. Apps don’t receive your fingerprint or face data. The system only tells the app whether authentication succeeded
What happens if the biometric login fails?
If it fails, the app should offer another way to log in, like a password or PIN. Biometric failure is normal and expected, so a fallback is always part of the design.
Can users turn biometric login off later?
Yes. Users should always be able to turn it off from app settings or device settings. Biometric login is meant to be optional, not permanent.
Is biometric login better than passwords?
It’s not better in every situation. Biometrics are great for quick access, while passwords are still important for first-time login and account recovery. Most apps use both together.